Set up ISL Conference Proxy
Meet strict security requirements, plus enjoy privacy and full independence by installing ISL Online on your server(s). All remote connections are then established through the server(s) in your company, keeping all data such as user information or session history in a closed corporate environment.
Sign Up to Server License
Create Server License Account
1. Sign up to create an account (Skip this step if you already have an ISL Online account).
2. Login to your account via the ISL Online website. Click "Your Username" in the top right corner, then click "Server License" from the menu.
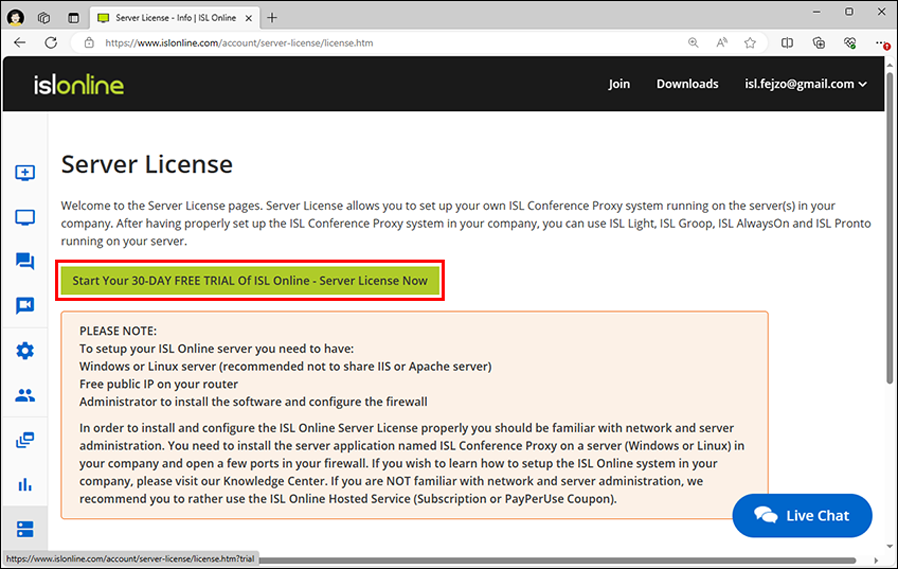
3. Click "start your 30-DAY FREE TRIAL of ISL Online - Server License now".
Server Requirements
Microsoft Windows
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows 10 (32-bit and 64-bit)
- Microsoft Windows Server 2012 R2
- Microsoft Windows 8.1 (32-bit and 64-bit)
- Microsoft Windows Server 2012
- Microsoft Windows 8 (32-bit and 64-bit)
- Microsoft Windows Server 2008 R2
- Microsoft Windows 7 (32-bit and 64-bit)
Linux
Linux Kernel 2.6.32 or newer and glibc 2.12 or newer (RHEL/CentOS 6.0 equivalent)
Hardware requirements
CPU
- Minimum: INTEL or AMD 1.4 GHz (x86 processor or x64 processor)
- Recommended: Multi-core CPUs, x64 processor, 3 GHz or faster
Memory
- Minimum: 2 GB RAM
- Recommended: 4 GB RAM (standard) or 8 GB RAM (Corporate Server License)
Available disk space
- Minimum: 10 GB
- Recommended: 20 GB (standard) or 100 GB (Corporate Server License)
Hardware virtualization: We also support virtualization environments (such as Hyper-V, Xen, VMware) with one of the supported operating systems installed.
Important: Avoid running antivirus clients on your Windows servers!
If you have an antivirus program installed on your Windows server, consider uninstalling it in order to prevent any interference with the ISL Conference Proxy operation and achieve best performance.
Many antivirus programs add hooks for various system calls (file access, network send/receive etc.) which can have an impact on performance or even cause slowdowns/issues during operations.
If you are not able to run your Windows server without an antivirus client you should add the ISL Conference Proxy directory (C:\Program Files\ISL Conference Proxy) to the whitelist and disable all real-time scanning for that directory and all sub-directories within it.
Reverse Proxy: ISL Conference Proxy 4.0.0 and later includes support for reverse proxy. If you plan to position the server behind an existing enterprise network security device such as F5 or a similar reverse proxy, please refer to the Reverse Proxy Manual.
Initial Setup
1. Define Server
First you need to add a server. Follow these instructions to find out how it's done.
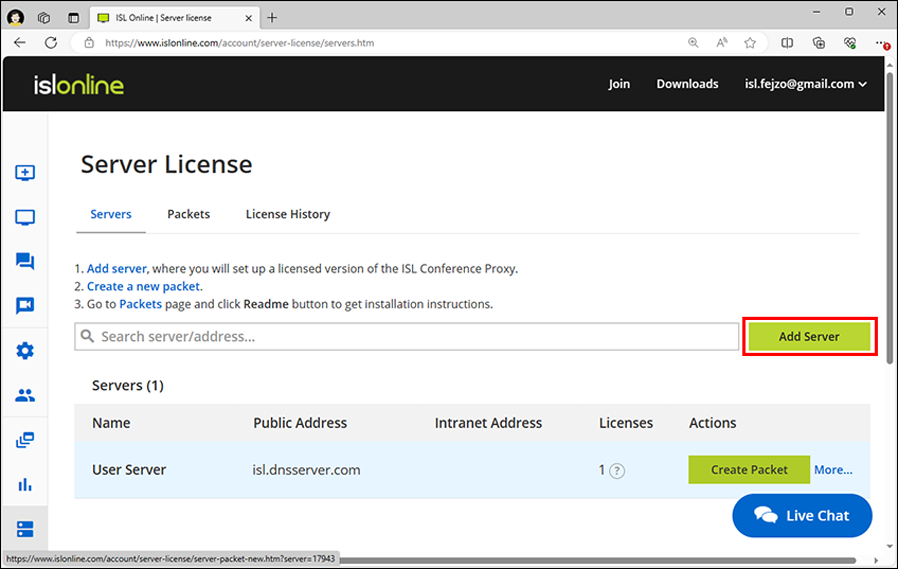
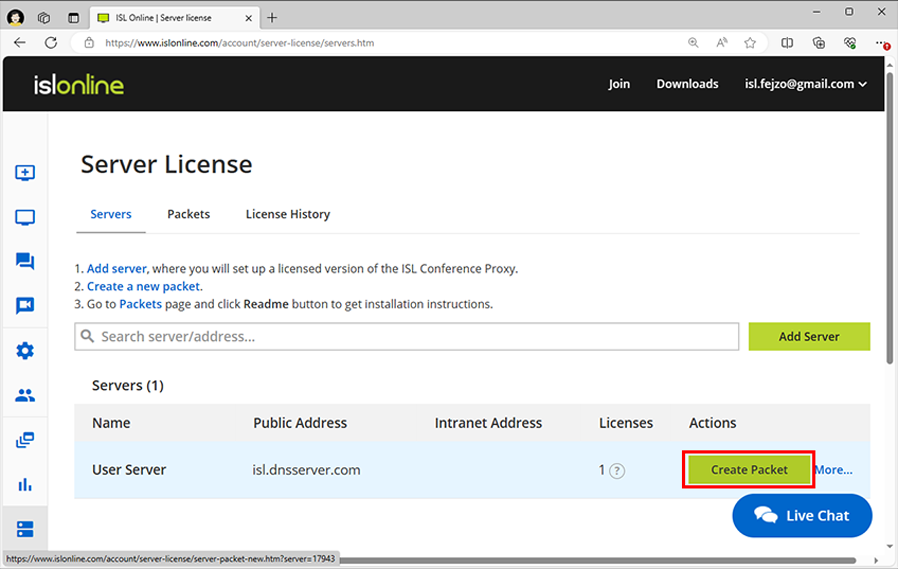
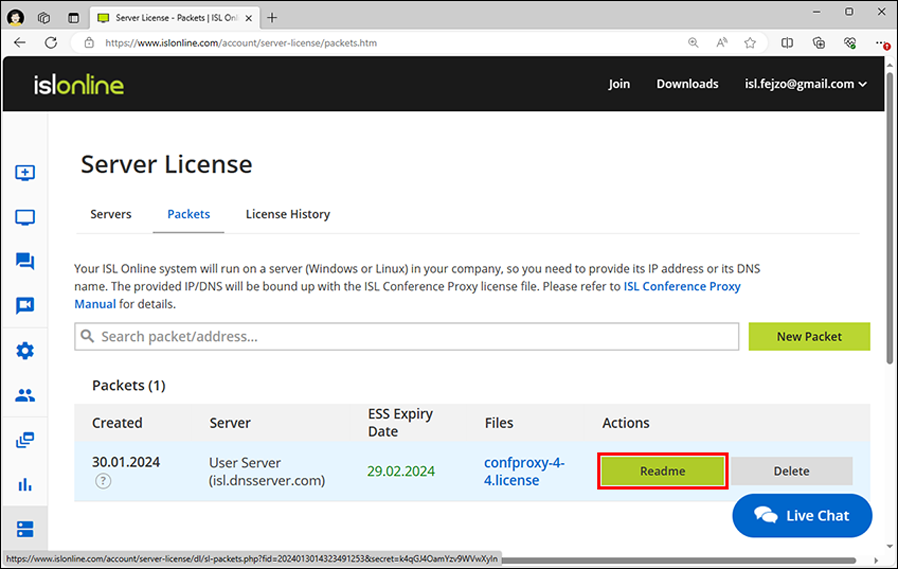
2. Create Packet
Next, you'll need to create a packet for your server. Follow these instructions to find out how it's done.
3. Assign License
Assigning a license means linking a license to the specified server. This installation guide assumes that you will assign at least one ISL Online Server License to a previously defined server.
Note: This step can be skipped for server trial users.
Installation
1. Download ISL Conference Proxy Installer
Windows:
64-bit: https://www.islonline.com/system/installer_latest_win64
Linux:
64-bit: https://www.islonline.com/system/installer_latest_linux64
Windows:
Note: If your server is running Windows Server Core, please proceed to the following topic: Installation on Windows Server Core
Linux:
Note: If your server does not have a graphical user interface, follow steps 1 and 2 and then run the command confproxyctl headless where you will be able to change the ISL Conference Proxy admin password (default is asd) and to specify trusted networks for web administration. After that, please perform the remaining steps (starting with step 3) from a computer with a graphical user interface that is within the specified trusted network. Replace localhost in the address with the appropriate server address for your situation. An alternative is to create an ssh tunnel to your server's local port 7615 and access the web administration through the created tunnel.
2. Run ISL Conference Proxy Installer
- Windows: You should login as the computer administrator or have the administrator password ready. Find the file in the download folder and run it. Follow the installation wizard for installation.
- Linux: cd to download folder and enter:
sh ISL_Conference_Proxy_4_4_2044_21_linux64.bin
3. Open ISL Conference Proxy Administration
Open web administration, which is available at address http://localhost:7615/conf
4. Login to ISL Conference Proxy Administration
Default username: admin
Default password: asd
5. Select Basic configuration and enter all necessary fields.
Note: We advise you to fill in the E-mail setup section so that ISL Conference Proxy will be able to send status information to your e-mail and inform you about critical events, session invitations etc.
6. Select Licenses and upload the license file (confproxy-4-x.license).
7. Select Online update and download all necessary software components (ISL Light, ...).
Note: You may need to perform the Online update a few times, until all Conference Proxy components are updated. Please repeat the step 6 until there are no more updates available.
Configure the Firewall
ISL Conference Proxy requires several TCP ports to operate properly. We advise you to open ports 80, 443 and 7615 in your firewall. If you have a web server running on ports 80, 443 or both of them, ISL Conference Proxy notifies you about binding errors on all conflicting ports.
You might be getting errors about binding ports like the example below, depending on your current network and server settings.
Server (-1) reports errors: - Cannot bind TCP port 80
All these errors regarding binding ports (if any) should be resolved after configuring your firewall.
Best Practices
Whenever you deploy ISL Conference Proxy to a server, no matter if it is a Linux or Windows machine, you should make sure it is as secure as possible.
Some of these steps are quite general (not ICP-specific, not OS-specific), but we will list them anyway for reference:
1. Reduce the possible attack surface, i.e. disable (or even better, uninstall if possible) everything you do not need on the server (ICP does not have any external dependencies such as web server, database etc., so you do not need those roles).
2. Keep the server (OS and installed programs) up to date.
3. Allow access only to ports you need for ICP (check user manual for more information) and your access (SSH, RDP), drop/block the rest.
4. Use strong passwords for both the machine itself and for ICP administration.
5. Make sure you have configured the mail server and related settings so that you will receive error reports and notification emails from ICP:
Configuration -> General -> Outgoing mail server (SMTP)
Configuration -> General -> SMTP port
Configuration -> General -> Default e-mail from address
Configuration -> General -> System e-mail goes to
6. Enable SSL for ICP web pages - check user manual for more information.
7. Check the SSL protocols and cipher suite settings and make sure they match your security and compatibility requirements. Default protocol and cipher suite settings should be a good starting point and in case you have no specific requirements you should leave them at their default values.
Important: Before making any permanent changes to protocol or cipher suite settings we strongly suggest testing all your main use cases to make sure these changes will not break backward compatibility where this is not acceptable. Suggested further reading:
https://en.wikipedia.org/wiki/Transport_Layer_Security#Applications_and_adoption [wikipedia.org]
https://wiki.mozilla.org/Security/Server_Side_TLS#Recommended_configurations [mozilla.org]
8. By default, ICP administration is only possible from localhost - if the plan is to access the ICP administration machine via RDP or through an SSH tunnel, you can keep this default setting. If you would like direct access to ICP administration from another machine, make sure you have an SSL certificate on your ICP and you force SSL for administration:
Configuration -> Security -> Must use SSL for administration: Yes
Then you can set the trusted network address(es) and/or subnets that should have access to the ICP administration:
Configuration -> Security -> Allowed IP addresses for administration
9. Force SSL for all ICP user web pages, websockets and webapi:
- Configuration -> Security -> Redirect HTTP to HTTPS for all user web pages: Yes
- Configuration -> Security -> Require HTTPS for WebSockets when HTTP to HTTPS redirect is enabled: Yes
- Configuration -> Security -> Require HTTPS for WebAPI when HTTP to HTTPS redirect is enabled: Yes
- Configuration -> Security -> Require HTTPS for WebAPI2 when HTTP to HTTPS redirect is enabled: Yes
10. You might want to generate custom crypto keys (software signatures, client to server, client to client), you can do it here:
Configuration -> Advanced -> Security
11. Last but not least, make regular backups.
Top Questions
-
How do I access ISL Conference Proxy administration?
Please go to https://localhost:7615/conf using your web browser.
-
What is the default admin password?
Default admin password is asd - please change it after the installation for security purposes.
-
How do I reset my admin password?
Please follow the appropriate procedure based on your operating system:
Windows
Please open the ISL Conference Proxy installation directory (default: C:\Program Files\ISL Conference Proxy) and run reset_adminpwd.bat as Administrator. This will set the admin password back to asd.
Linux
Please run the the following command from a terminal on your server: confproxyctl headless It will ask you for a new ISL Conference Proxy admin password and you will be able to specify trusted networks for web administration.
-
How can I update my ISL Conference Proxy?
Please refer to the Online update or Manual update chapters in the ISL Conference Proxy manual.
-
What ports needs to be opened, which protocol and direction?
ISL Conference Proxy server: 7615 (TCP, incoming), 443 (TCP, incoming) and 80 (TCP, incoming)
ISL Light requires at least one of the following ports - 7615 (TCP, outgoing), 443 (TCP, outgoing), 80 (TCP, outgoing)
Please note that you can change these ports in the ISL Conference Proxy administration.
If port 80 is already taken (e.g. if you are running IIS or Apache on the same IP), please go to Configuration - General - HTTPT ports and remove port 80 from the list and ISL Conference Proxy will not try to bind that port. If possible, please have a separate IP address for ISL Conference Proxy and all three ports available in order to allow most users to connect.
-
Is there any way I can see which service is using the 80 or 443 port?
You can try cmd line utility netstat -ano. Another option is to find processes with pid in netstat in task manager. You can also check tcpdump from sysinternals. Please refer to user manual.
-
Is it better to have ISL Conference Proxy running on Linux or Windows?
Whatever system suits you better. Performance wise, there are no differences between running ISL Conference Proxy on Linux or Windows. Please refer to server requirements.
-
Can ISL Conference Proxy run in a virtual machine?
Yes, ISL Conference Proxy can be installed in a virtual machine as long as it is running one of the supported operating systems. Please refer to system requirements for more information.
However, please keep in mind that a virtualization environment requires proper setup and represents another possible point of failure.
-
How do I install a custom SSL certificate?
Please refer to this topic in the manual: Enabling SSL.
-
How can I move my existing ISL Conference Proxy installation to a new server?
We recommend using the functionality of the backup module to perform a server migration. This approach also allows you to migrate across platforms, i.e. from a windows server to a linux server or vice-versa. Please refer to user manual for more information.
-
Can I integrate ISL Conference Proxy with LDAP / SAML / FreeRADIUS / Radius / Active Directory / eDirectory ?
Yes, please refer to user manual.
-
Is there a way to bulk-import user details?
Yes, it is possible to do so using XMLMSG protocol. Please send an e-mail to support@islonline.com and we can write you a short guide.
Continue Reading: Security Tips